- news
- AUDITING
Using audit data analytics in performing a risk assessment procedure
Please note: This item is from our archives and was published in 2017. It is provided for historical reference. The content may be out of date and links may no longer function.
Related
PCAOB works to form Inspections Modernization Council
What CPA.com’s CEO sees next for AI, tax, and the profession
How to monitor a firm’s system of quality management
TOPICS
The rapidly evolving discipline of data analytics holds substantial promise for auditors in their constant quest to provide clients with greater quality in the engagements they perform.
Audit data analytics provides auditors with an opportunity to review and analyze a larger population of data in order to identify information used to support audit procedures. The potential for deriving new insights from this process is immense, and auditors and their clients will reap the benefits.
Benefits of audit data analytics include:
- An improved understanding of an entity’s operations and associated risks, including the risk of fraud.
- Increased potential for detecting material misstatements.
- Improved communications with those charged with governance of audit clients.
The AICPA’s new Guide to Audit Data Analytics provides guidance that enables practitioners to use these developing techniques in their service to their clients. The guide is available for purchase from the AICPA Store. The following excerpt from the guide provides five basic steps an auditor might use in planning, performing, and evaluating the results of using an audit data analytic (ADA) in performing risk assessment procedures and to assist when forming an overall conclusion:
1. Plan the ADA.
a. Determine the financial statement items or accounts, or disclosures, and related assertions and the nature, timing, and extent of the population to which the ADA will be applied.
b. Determine the overall purpose of the ADA (for example, whether it is to be used in performing a risk assessment procedure, a test of controls, a substantive analytical procedure, a test of details, or in procedures to help form an overall conclusion from the audit).
c. Determine the specific objectives of the ADA (within the context of its overall purpose).
d. Determine the data population to be analyzed or tested using the ADA, including, for planning purposes, preliminary consideration of matters likely to affect the relevance, availability, and reliability of that data.
e. Select the ADA that is likely best suited for the intended purpose and objectives.
f. Select the techniques, tools, graphics, and tables to be used.
2. Access and prepare the data for purposes of the ADA.
3. Consider the relevance and reliability of the data used.
4. Perform the ADA.
a. If the initial results of the ADA indicate that aspects of its design or performance need to be revised, make appropriate revisions and reperform the ADA.
b. If the auditor concludes that the ADA has been properly designed and performed, and the ADA has identified items that warrant further auditor considerations, plan and perform additional procedures on those items consistent with achieving the purpose and specific objectives of the ADA. (Note: See the flowchart in Exhibit 2-2 and supporting material for addressing circumstances when a large number of such items has been identified.)
5. Evaluate the results and conclude on whether the purpose and specific objectives of performing the ADA have been achieved.
a. If the objectives have not been achieved, plan and perform different procedures to achieve those objectives.
Documentation: The auditor should comply with the relevant documentation requirements in generally accepted auditing standards when performing each step and related procedure. Paragraph .33 of AU-C Section 315 sets out requirements regarding the documentation of risk assessment procedures. Paragraphs 1.48–1.56 of this guide discuss matters related to documenting ADAs.
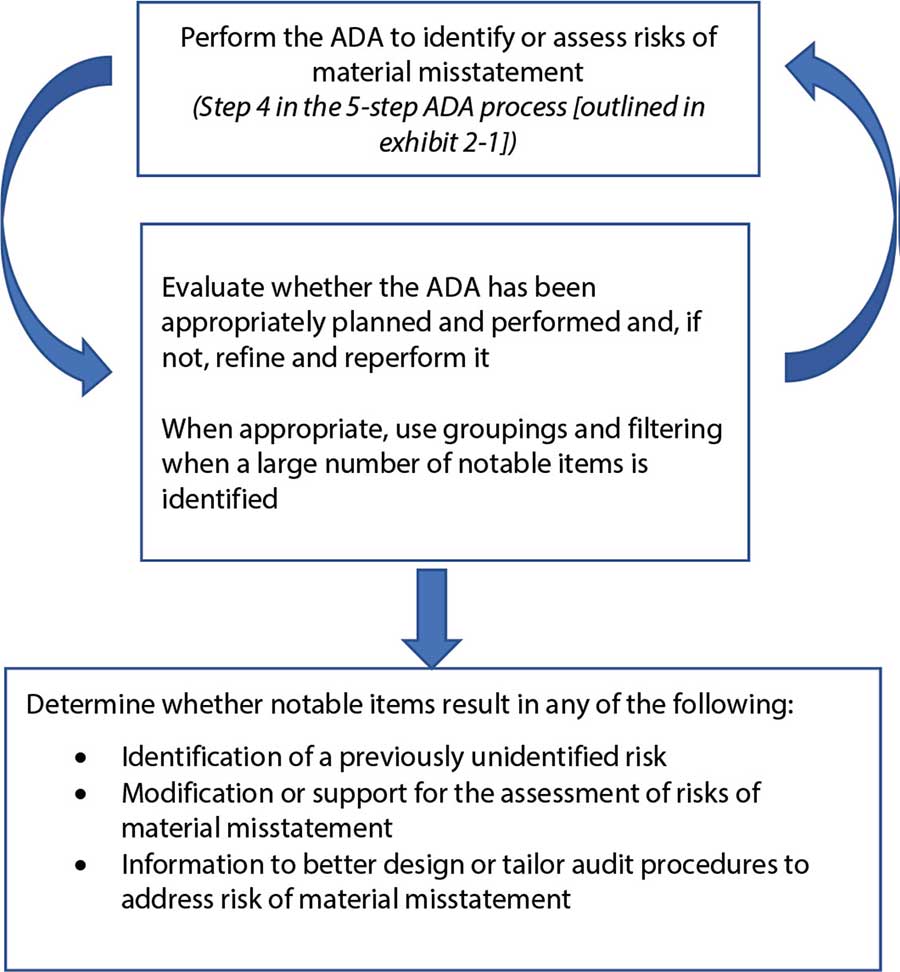
Exhibit 2-2
Process to Identify and Address Notable Items When Using an ADA in Performing a Risk Assessment Procedure.
Using an ADA in performing a risk assessment procedure may result in the identification of one or more notable items or items that may be problematic. To address these items identified the auditor might follow the process described below.
—Ken Tysiac (Kenneth.Tysiac@aicpa-cima.com) is a JofA editorial director.


















