- column
- TECHNOLOGY Q&A
Protect your online privacy with a VPN
Please note: This item is from our archives and was published in 2018. It is provided for historical reference. The content may be out of date and links may no longer function.
Related
What CPA.com’s CEO sees next for AI, tax, and the profession
AI for CPAs: From efficiency tool to decision engine
9 tips to write more effective AI prompts
Q. What should we do to keep our company’s online activities private while using our computers and smartphones?
A. You’ve probably seen a few Hollywood movies in which an attempt to trace the physical location of an online hacker is thwarted as the hacker’s IP address momentarily pinpoints him or her in a faraway location in, say, Japan, then Europe, Singapore, Australia, and so on. This type of stealth online presence can theoretically be accomplished using a virtual private network (VPN) to connect through additional VPNs around the world, masking the origin of an online connection. You’ll probably admit this crafty measure makes the movie villain appear formidable and tech-savvy.
Movie effects aside, many U.S. companies use this same type of VPN technology to protect their online privacy, and you can, too. This measure will help prevent third parties from tracking your location’s IP address, monitoring your web-browsing activities, intercepting your email messages, copying your uploaded or downloaded data files, or spying on your video conferences. Hiding your IP address using a VPN prevents data tracking from even your internet service provider, which can see nothing more than that you’re connected to the internet. Everything else — including your web searches, page views, email messages, and the new IP address you’ve been assigned by your VPN connection — is protected from prying eyes. (It is worth noting that while VPN service providers claim they don’t track or record your online activities, you are dependent on them to abide by their promises of secrecy and anonymity. The risk of a privacy breach may increase if the VPN provider is located in a country with fewer privacy protections or government-surveillance restrictions than the United States.)
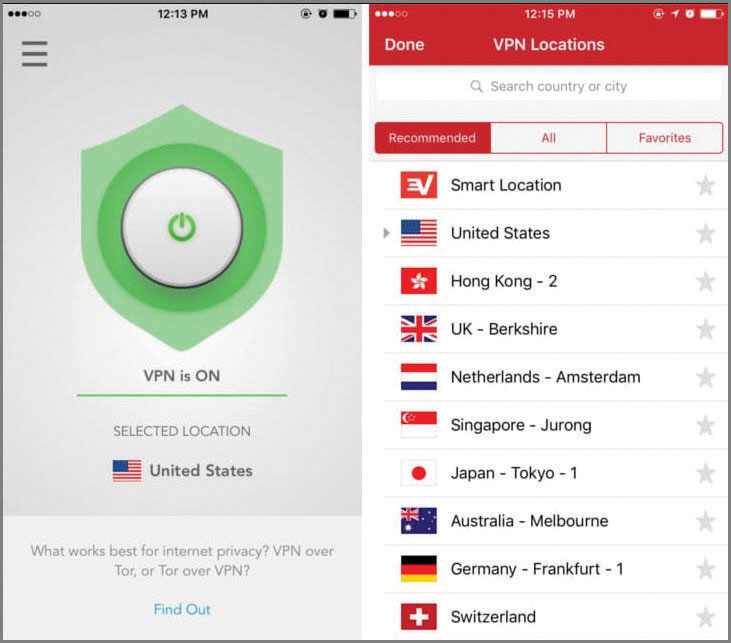
The easiest and least expensive way to set up a VPN is to subscribe to a VPN service provider. There are many providers to choose from; some examples are listed at the end of this item. For example, ExpressVPN is a VPN solution that is relatively inexpensive and easy to set up. To subscribe to the ExpressVPN service, visit expressvpn.com, and click the Get ExpressVPN button. Select a pricing option ($8.32 per month for 12 months, $9.99 per month for six months, or $12.95 for a single month, as of April 2018). Follow the online instructions to sign up for ExpressVPN and obtain an activation code. Continue by downloading the installer software for your operating system platform (Windows, Apple, Android, etc.). The software will download and run automatically, then you will be directed to set up a username and password. Once you log in, the installer software will display a settings page, where you will be asked if you want to install the default profile; select Install to complete the setup process. This process will make dozens of worldwide ExpressVPN servers available to you, as pictured at the bottom of the page.
Select any ExpressVPN server to connect to the internet through that server. Once connected, your computer’s IP address is hidden. At that point, no third parties will be able to monitor your browsing, and your online activities will be encrypted (including email, uploads, downloads, searches, browsing, etc.). In effect, this solution lets you access the internet anonymously from your computer. The installation process is similar for other platforms, such as Windows, Linux, and Android smartphones — just download the relevant installer software and use the same activation code to implement VPN access to the internet on your other devices, such as your home computer or smartphone.
In addition to ExpressVPN, popular VPN service providers include PureVPN (purevpn.com), NordVPN (nordvpn.com), ZenMate (zenmate.com), Hotspot Shield (hotspotshield.com), and CyberGhost VPN (cyberghostvpn.com). The “Checklist for Evaluating VPN Service Providers” highlights features to consider when evaluating VPN service providers; this information can usually be obtained from vendor websites.
Note that a VPN connection will not protect you from key-logging software or data-mining viruses that are already installed or may become installed on your computer(s) or smartphone(s); those types of hacking tools can capture data directly from your device and transmit them through your VPN connection to nefarious destinations.
Checklist for evaluating VPN service providers
1. Installation software for easy setup. Rather than forcing you to configure your computer’s settings manually (a complicated process), installation software asks you a few basic questions and then makes all the necessary configuration and setup changes for you.
2. 256-bit encryption. This indicates that your online activities are protected using technology equivalent to the type of encryption the U.S. military uses to protect communications it classifies as “Top Secret.”
3. More than 500 servers. This indicates the size of the VPN service provider; theoretically, providers with more servers are more established, and they are more likely to provide a full range of technologies for protecting your anonymity.
4. No logging. This means that third-party websites and internet service providers are unable to log (or record) your online activities.
5. Kill switch. This means that if attempts to log your activities are detected and the VPN’s privacy measures are seriously threatened, your entire connection to the internet is immediately cut (killed) to protect you from hackers or unauthorized users.
6. P2P downloading allowed. This technology enables you to upload or download files securely, even though you are connected to the internet via an anonymous VPN connection.
7. Number of devices supported. This measure indicates how many devices are included in your VPN subscription. For example, you may want to surf the internet securely using your work computer, home computer, and smartphone, which means you’ll need three connections. Many VPN services include up to five devices as a standard option.
8. Number of simultaneous connections allowed. This indicates how many VPN-connected devices you can use simultaneously.
9. High-speed connection for video streaming. This means high-speed internet is supported so you can participate in video conferences or watch streamed movies on Netflix or Hulu.
About the author
J. Carlton Collins (carlton@asaresearch.com) is a technology consultant, a conference presenter, and a JofA contributing editor.
Submit a question
Do you have technology questions for this column? Or, after reading an answer, do you have a better solution? Send them to jofatech@aicpa.org. We regret being unable to individually answer all submitted questions.


















